Most professionals affected by MAR know that, to be classified as inside information, the information needs to be considered precise with a likely significant price effect and not public. Still, a question recently debated is what is considered “public” data.
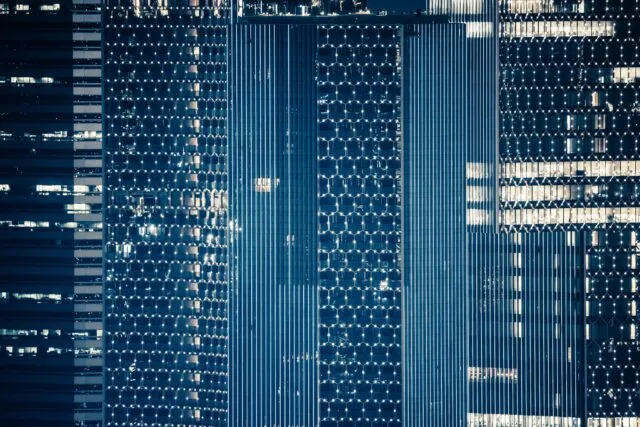
The Role of Alternative Data
This question has become especially relevant given the increasing use of different forms of alternative (big) data. Such data can include:
- Advanced Internet of Things (IoT) data
- Website scraping results
- Processed social media data
- Advanced transactional/financial institution data
- Detailed sales data from major actors in specific fields
- Advanced shipping data
- Credit card transactions
- Processed satellite information data
- Mobile phone location data
Regulatory and Reputational Risks
Regardless of the reputational and regulatory risks related to Internet and privacy legislation (such as GDPR), professionals are also concerned with the MAR perspective and the associated insider trading and securities law risks. The originality level of processed big data combined with high demand creates a risk of operating in a grey area, potentially bordering on a breach of confidentiality or fiduciary duties.
A pertinent question in this context is whether such information can be acquired or purchased by anyone or if there are limitations. Sometimes, data providers sell certain data with exclusivity agreements, available to only a few customers or sophisticated investors. The underlying pitch for such data is that the end-user will gain an edge by accessing exclusive information.
Due Diligence for Acquired Data
Due diligence is essential to ensure that acquired data has been legally produced. This includes ensuring that all data providers respect rules related to copyright, confidentiality, intellectual property rights (IPR), and terms of use.
Borderline Cases and Data Sources
Borderline cases may arise with processed data derived from advanced surveys and interviews. Such data may not always be public. Additionally, some data produced by third-party providers—such as intelligence or private investigations firms—may involve non-public data.
Inside information can originate from a wide range of sources beyond the issuer, including:
- Rogue employees, consultants, or stakeholders
- Competitors
- Leading analysts or journalists
- Regulators
Level Playing Field Principle
A fundamental principle of EU legislation is maintaining a level playing field and avoiding unfair advantage. Combined with the relatively new MAR, these principles have resulted in uncertain practical applications, unlike the more established US Material Non-Public Information (MNPI) practices.
Practical Approach
Given these risks and legal uncertainties, the most prudent approach is to exercise caution. In some cases, it may be straightforward to determine that data is public. Treating the data as inside information is advisable in others, where significant concerns exist. In borderline cases, the commercial imperative for using relevant information may necessitate a careful analysis by external legal experts.
FSMA vs Nyrstar: what the ruling means for delayed disclosure and insider lists
European market-abuse enforcement does not happen in isolation. Although MAR applies directly in every EU member state, day-to-day expectations are shaped by how regulators interpret and apply it in real cases. Court […]
FSMA vs Nyrstar: what the ruling means for delayed disclosure and insider lists
European market-abuse enforcement does not happen in isolation. Although MAR applies directly in every EU member state, day-to-day expectations are shaped by how regulators interpret and apply it in real cases. Court […]
The Essential Guide to Writing and Enforcing a Code of Conduct
Every successful organisation needs a strong code of conduct to set the tone for ethical behaviour and guide employees in their daily decisions. A well-crafted code of conduct isn’t just a document […]
Code of Conduct vs. Code of Ethics: What’s the Difference and Why It Matters
When organisations embark on creating policies for ethical conduct, two terms often emerge: code of conduct and code of ethics. These phrases are sometimes used interchangeably, which can cause confusion. In this […]
Conflict of Interest Explained: Types, Policies, and Real Examples
Learn how to identify and manage conflicts of interest using effective policies and compliance tools to prevent risk and ensure accountability.